This is a demonstration on how easily client side content can be injected at runtime. One does not have to architect posts or recreate content and repost. The easiest way to do this that I know of is with a firefox plugin called Chickenfoot, http://groups.csail.mit.edu/uid/chickenfoot/install.html. With it you can script navigation, user interaction, changes to DOM, etc.
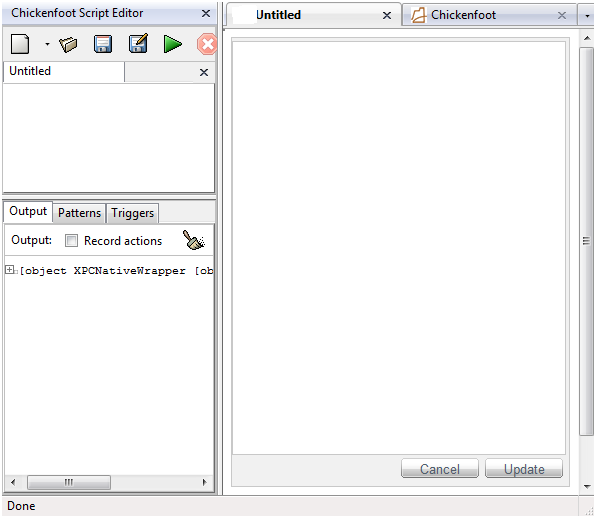
On to the demo at hand. For this I have taken an instance of RadEditor, a WYSIWYG html editor and disabled almost everything. So if the client side restrictions were 'strong' the user wouldn't be able to do anything but insert plain text into the region on the page. The screenshot below shows the initial setup.
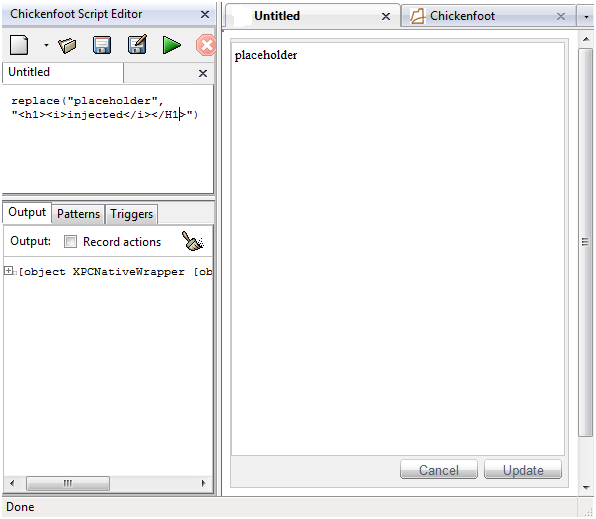
For a real quick demonstration, enter 'placeholder', or any placeholder into the region. Now write the script with chickenfoot to replace it with your html. Such as :
Running this results in the following:
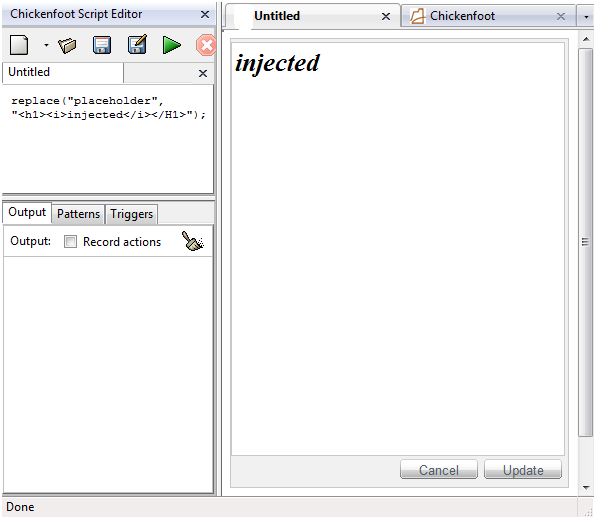
Now granted, this is nothing impressive; we have modified the content within our browser, who cares? Well, that depends on the who programmed the site. If they are assuming the control is taking care of injection they might be in for a surprise. The lesson? Always validate server side for any input imaginable, anything can be posted… and it just got easier to pull off.
And in case it hasn't come to mind, you could very easily inject a full screen div to hijack the page the html is shown on. I doubt someone would go through the trouble for some bolding tags.